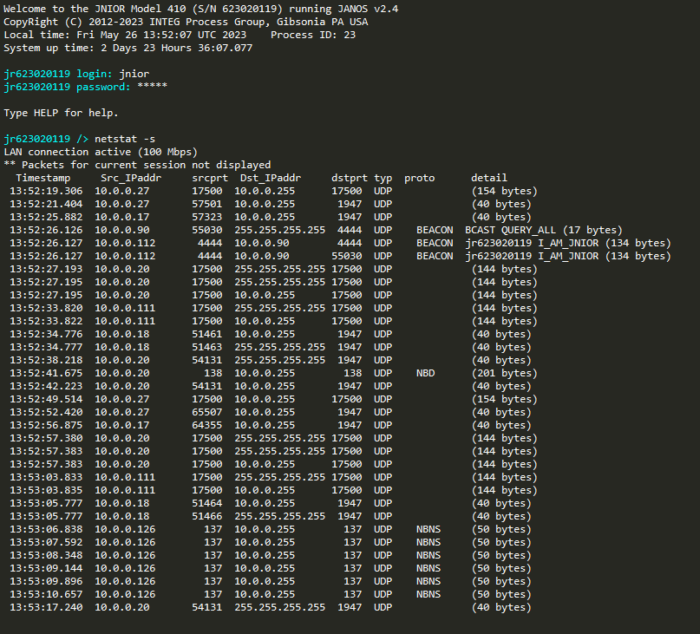
Netstat -s
While the netstat command has had the ability to record data being transmitted between Series 4 JNIORs and other devices for a set duration, the netstat -s command allows the JNIOR to display that information in real time. netstat -s will run a network sniffer and display all data communication connections except for the session being used to run the network sniffer.
What is a network sniffer?
A network sniffer is a tool used to analyze data packets traveling on a network. This will allow you to monitor devices connecting to the JNIOR along with the network packets they are sending to and from the JNIOR. So to start, if you want to quickly observe the list of devices that have network traffic with the JNIOR, instead of taking a whole network capture you can just use netstat -s. Once the netstat -s command is running, any keystrokes in the terminal will terminate the network sniffer.
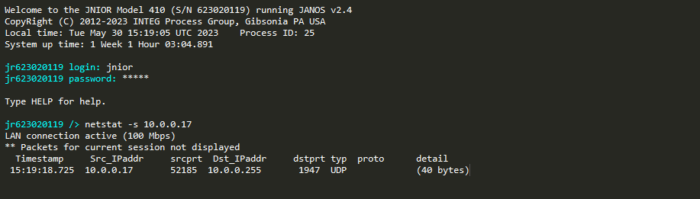
IP Filtering
When using the netstat -s command, there is also an option to provide a filter after the command. This is useful because depending on how the JNIOR is configured, it may have tons of data being sent back and forth between different devices. Once the filer is applied, it will only show data within the filter’s parameters. For example, in the picture below the filter provided was an IP Address. So the netstat -s command will only show devices being connecting to the JNIOR with that IP address.
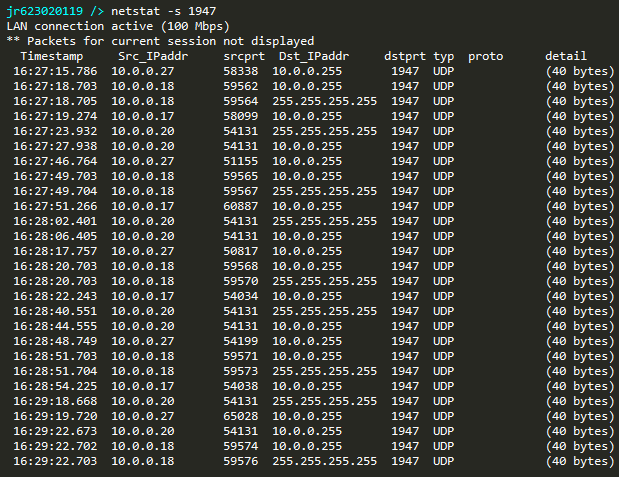
Port Filtering
The netstat -s command can also use port numbers for the filter as well. Any device connecting with the JNIOR on the filtered port will have that connection displayed. The example below shows a port number being used as a filter for netstat -s.
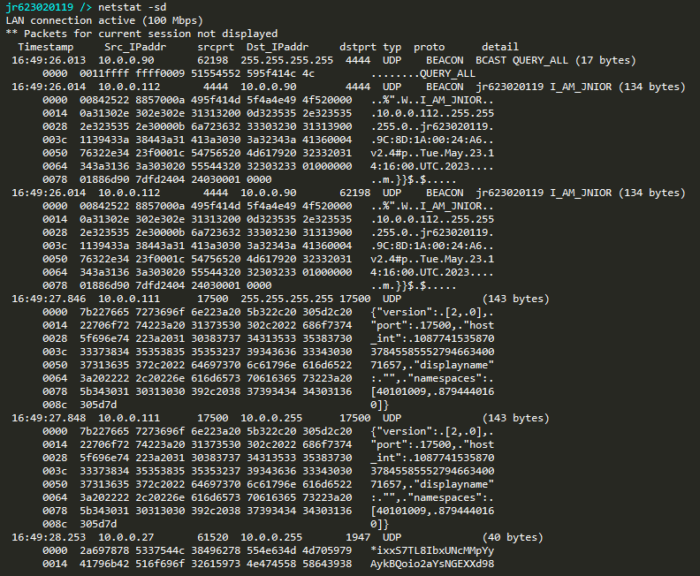
Netstat -sd
Additionally, another command option for netstat is to use netstat -sd. This command not only activates the network sniffer and displays the devices that are communicating with the JNIOR, but also displays the packet data being sent between the them as well!